Short version
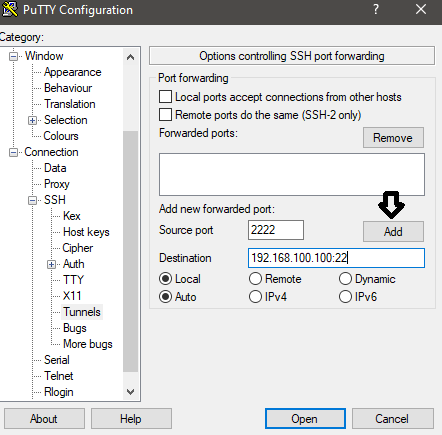
Source port is the local port you connect to.
Destination is relative to the system you're SSHing to in <IP address>:<port> format.
See Tunnel Setup for settings screenshots.
Why?
SSH tunnels can be used as an intermediary for systems you can't reach. This can be useful for hosted environments with private networks.
For example, if you have SSH access to a system (bastion) on both public and private networks you can use an SSH tunnel to access systems on the private network.
Example
Here's an example with screenshots.
Imagine if you will, two networks (10.0.0.x and 192.168.100.x) that can't talk to each other.
I'm on the 10 network with others users that can't be trusted.
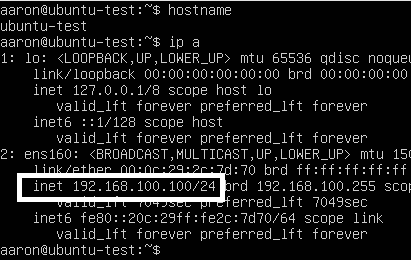
The 192 network has a system (ubuntu-test) that I want SFTP access to.
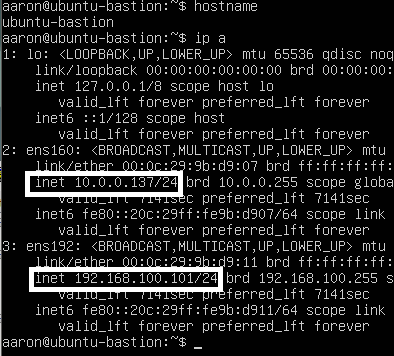
I have SSH access to a system (ubuntu-bastion) on both the 10 and 192 networks.
I'm using vlans to separate the servers here so I could just add my machine to the other network. Think of the 10 network as the internet and 192 as a private network for this example.
I can't access 192.168.100.100 on port 22 (SFTP) from my machine.
I'm using telnet to check the port. Not related to the SSH tunnel.
![]()
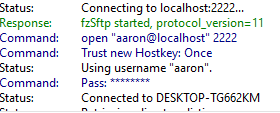
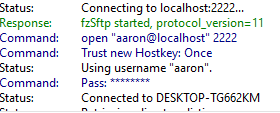
After setting up the SSH tunnel I can access SFTP (port 22) on the system in the 192 network.
If you only need SSH access to another system consider using an SSH command in the Remote Command setting under Connection > SSH. There are a few considerations to this depending on how you connect which is out of the scope for this post.
Tunnel Setup
Use the session settings for the bastion system as usual.
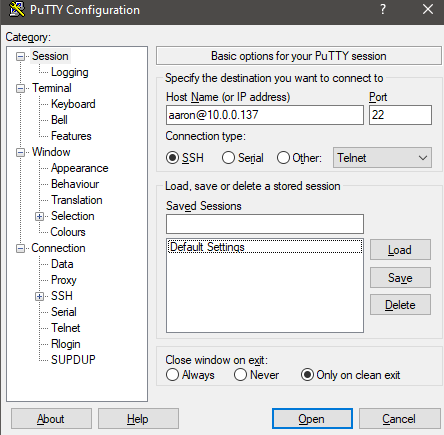
Go to Connection > SSH > Tunnels
Source port: Port used for connecting to the tunnel. You will connect to this port on your local system.
Destination: Destination in <IP address>:<port> format relative to the system you're connecting to with putty.
Click Add to save.
You will see the source port and destination in the forwarded ports box after clicking Add.
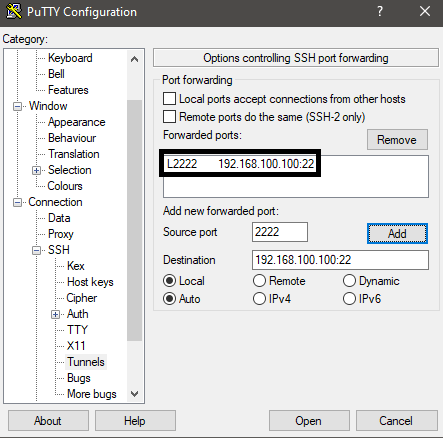
Click Open to connect.
The SSH session will prompt as usual. Log in with username/password if needed and leave the session open to keep the tunnel active.
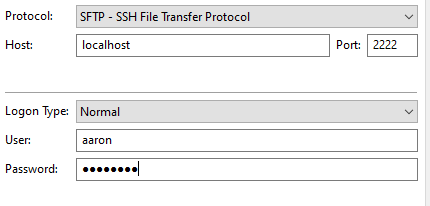
You can now connect to localhost:2222 to reach 192.168.100.100 on port 22.